- Splunk Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- How to show timechart and timewrap of business hou...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
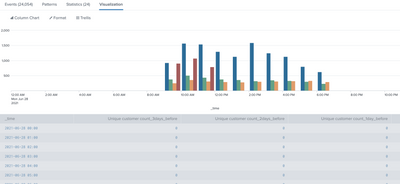
How to show timechart and timewrap of business hours
I am trying to compare count of events with previous days within business hours, here is my query
index=abc
| search "userId:"
| where date_hour>=9 AND date_hour<=17
| rex field=message "userId: (?<customerId>.*)"
| timechart span=1h dc(customerId) as "Unique customer count"
| timewrap d
I am trying to see the chart data only between 9AM to 5PM, but it is showing data (bar chart) on 24hr scale with blank before 9AM and after 5PM.
How can I adjust the query or time picker to get the desired output ?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Can you try this,
index=abc earliest=@d+9h latest=@d+17h "userId:"
| rex field=message "userId: (?<customerId>.*)"
| timechart span=1h dc(customerId) as "Unique customer count" ---
An upvote would be appreciated and accept solution if it helps!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This is working fine for one day's data, even my search range is last 7days it is just giving today's data only.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Can you try this
index=abc "userId:"
| where date_hour>=9 AND date_hour<=18
| rex field=message "userId: (?<customerId>.*)"
| timechart span=1h dc(customerId) as "Unique customer count"---
An upvote would be appreciated if it helps!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It is still giving data from 00:00 to 23:00
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I wish this can be done better, however date_hour i understood its not being extracted by Splunk from _time but actually its from original event FYI. About default fields (host, source, sourcetype, and more) - Splunk Documentation
Following should work, extracted hour from _time. you would find events upto 17:59 as time_hour = 17, you need to further change this condition using time_min
index=abc "userId:"
| eval time_hour=strftime(_time, "%H") , time_min=strftime(_time, "%M")
| where time_hour >=9 AND time_hour<=17
| rex field=message "userId: (?<customerId>.*)"
| timechart span=1h dc(customerId) as "Unique customer count"
---
An upvote would be appreciated if it helps!