Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
Splunk Search
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Showing results for
- Splunk Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- How to rename table field names dynamically in a s...
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How to rename table field names dynamically in a search?
jackson1990
Path Finder
05-31-2015
09:55 PM
Sample EventList for my scenario given below:
ID=1 | Name=sankar | Age=20 | Dept=Computer science | Programming=60 | DataStructure=70 | RDBMS=80 | Compiler=75
ID=2 | Name=Akash | Age=25 | Dept=Mechanical | SolidMechanics=80 | ThermoFluidMechanics=65 | Manufacturing=90
ID=3 | Name=Sathish | Age=18 | Dept=Computer science | Programming=70 | DataStructure=84 | RDBMS=90 | Compiler=85
ID=4 | Name=Arun | Age=24 | Dept=Mechanical | SolidMechanics=70 | ThermoFluidMechanics=55 | Manufacturing=80
ID=5 | Name=Kavya | Age=30 | Dept=Electrical | PhysicalOptics=80 | InformationSecurity=75 | Nanophotonics=90 | ImageProcessing=85 | NonlinearSystemTheory=85
ID=6 | Name=Kaveri | Age=24 | Dept=Computer science | Programming=70 | DataStructure=50 | RDBMS=50 | Compiler=85
ID=7 | Name=Hema | Age=25 | Dept=Electrical | PhysicalOptics=60 | InformationSecurity=85 | Nanophotonics=90 | ImageProcessing=75 | NonlinearSystemTheory=68
ID, Name, Age and Dept fields will be present in all Events without any change in Name, whereas the Courses differs w.r.t Dept.
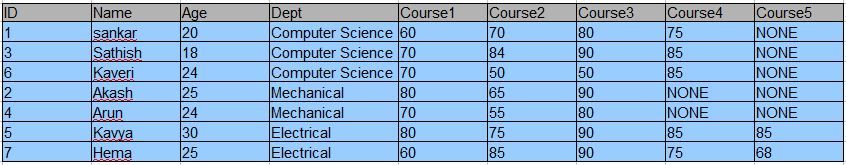
Resulting Table, i am Excepting as
Instead of the fields as course name for each dept, it has to be renamed as Course1, Course2 etc...
What is the splunk search I need to use to retrieve the above result?
I have tried with the search below, but didn't get the proper result:
index="college_index" | table ID,Name,Age,Dept,* | fields - source*,splunk_server_group,host,_raw date_*,index,linecount,punct,eventtype,splunk_server,_time,time*pos
It shows the table with courseNames only.
Any help will be much appreciated.
Thanks in advance
Get Updates on the Splunk Community!
Announcing Scheduled Export GA for Dashboard Studio
We're excited to announce the general availability of Scheduled Export for Dashboard Studio. Starting in ...
Extending Observability Content to Splunk Cloud
Watch Now!
In this Extending Observability Content to Splunk Cloud Tech Talk, you'll see how to leverage ...
More Control Over Your Monitoring Costs with Archived Metrics GA in US-AWS!
What if there was a way you could keep all the metrics data you need while saving on storage costs?This is now ...