- Splunk Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- How to merge events and show in tabular format?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello Splunkers ,
I am trying to see if I can merge the following events and show in a tabular format
sample event 1:
| 3/31/22 6:54:29.000 AM |
GB (ID 5): BSN: 15730946, BON: 699-01, BOAA: 01, GPN: 1395, GSN: 920-000
|
Sample event 2:
| 3/31/22 6:54:29.000 AM |
CPU (ID 0): BSN: 55506204BC, BON: 555.06901.0004, BOAA: 01, QPN: 16646, QSN: 001
|
Sample event 3:
| 3/31/22 6:54:29.000 AM |
CHASN: 166066
|
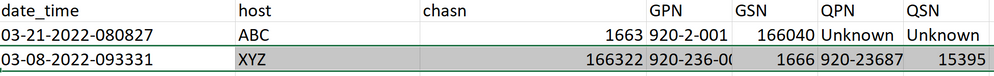
I want to merge all events which are coming from same host and same time and show in a tabular format. if there is no value for a particular field it should show UNKNOWN
time host CHASN GPN GSN QPN QSN
3/31/22
6:54:29.000 AM ABC 166066 1395 920-000 16646 001
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The host field is not very discriminating. Depending on the time window searched, there may be many sets of events from the same host and Splunk will combine them all into a single result.
See if this search gets you started. It presumes you already have the fields extracted.
<<your search for event 1>>
| append [ <<your search for event 2>> ]
| append [ <<your search for event 3>> ]
| stats values(*) as * by host
| table _time host CHASN GPN GSN QPN QSNIf you don't have fields extracted then you'll need to do that.
<<your search for event 1>>
| rex "GPN:\s*(?<GPN>\d+)"
| rex "GSN:\s*(?<GSN>\d+)"
| append [
<<your search for event 2>>
| rex "QPN:\s*(?<QPN>\d+)"
| rex "QSN:\s*(?<QSN>\d+)"
]
| append [
<<your search for event 3>>
| rex "CHASN:\s*(?<CHASN>\d+)"
]
| stats values(*) as * by host
| table _time host CHASN GPN GSN QPN QSNIf this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How does Splunk know how to combine those events? They should have at least one field in common, but appear to have no common fields. Don't try to merge events based on _time unless you can guarantee all three will be generated at the exact same millisecond.
If this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The three sample events have the same host..I am trying to merge them based on same host
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The host field is not very discriminating. Depending on the time window searched, there may be many sets of events from the same host and Splunk will combine them all into a single result.
See if this search gets you started. It presumes you already have the fields extracted.
<<your search for event 1>>
| append [ <<your search for event 2>> ]
| append [ <<your search for event 3>> ]
| stats values(*) as * by host
| table _time host CHASN GPN GSN QPN QSNIf you don't have fields extracted then you'll need to do that.
<<your search for event 1>>
| rex "GPN:\s*(?<GPN>\d+)"
| rex "GSN:\s*(?<GSN>\d+)"
| append [
<<your search for event 2>>
| rex "QPN:\s*(?<QPN>\d+)"
| rex "QSN:\s*(?<QSN>\d+)"
]
| append [
<<your search for event 3>>
| rex "CHASN:\s*(?<CHASN>\d+)"
]
| stats values(*) as * by host
| table _time host CHASN GPN GSN QPN QSNIf this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you..I did some tweaking and it helped