Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
Splunk Search
×
Are you a member of the Splunk Community?
Sign in or Register with your Splunk account to get your questions answered, access valuable resources and connect with experts!
Turn on suggestions
Auto-suggest helps you quickly narrow down your search results by suggesting possible matches as you type.
- Find Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- How to create a rex for search?
Options
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How to create a rex for search?
super_virus
New Member
08-06-2018
04:33 PM
I have the below log line:
Slow GraphQL query [8447ms]
How can I grab only the value "8447"?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
cpetterborg

SplunkTrust
08-06-2018
04:51 PM
Search-time? Index-time? Are all the events similar? Is that the whole event?
If you just want a search-time rex way with the example data being the whole event:
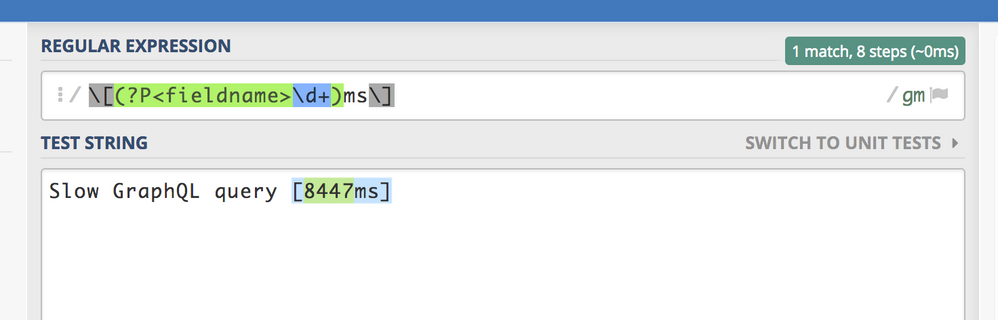
... | rex "\[(?P<ms>\d+)ms\]"
If it isn't the entire event, then use the field=yourfieldname option to the rex command.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
PowerPacked
Builder
08-06-2018
04:47 PM
Get Updates on the Splunk Community!
Splunk Observability as Code: From Zero to Dashboard
For the details on what Self-Service Observability and Observability as Code is, we have some awesome content ...
[Puzzles] Solve, Learn, Repeat: Character substitutions with Regular Expressions
This challenge was first posted on Slack #puzzles channelFor BORE at .conf23, we had a puzzle question which ...
Shape the Future of Splunk: Join the Product Research Lab!
Join the Splunk Product Research Lab and connect with us in the Slack channel #product-research-lab to get ...