- Splunk Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: How do I consolidate the count of similar valu...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
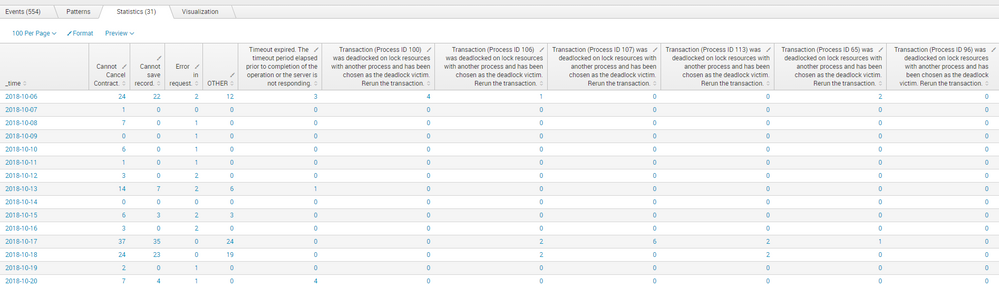
I have a Search that looks at some XML responses from an API and should create a time chart by the count of each type of error message.
I have a query that produces that result, but the issue I have is the transaction deadlock errors all represent the same type of error, but show as distinct columns since they have a unique "Process ID".
What I would like to do is consolidate the various Transaction Deadlock columns into one column and have the total count of all deadlock errors.
Query thus far:
index=my_favorite_index "message.location"="cancelContract"
| spath input=message.data.responseBody output=ResponseMessages path=soap:Envelope.soap:Body.CancelContractResponse.CancelContractResult.Messages.Message
| mvexpand ResponseMessages
| spath input=ResponseMessages
| timechart count by Text
Anyone have any ideas on how to accomplish this?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
We can try to group all the transaction into the same field so you don't have a column by Process Id ! 🙂
index=my_favorite_index "message.location"="cancelContract"
| spath input=message.data.responseBody output=ResponseMessages path=soap:Envelope.soap:Body.CancelContractResponse.CancelContractResult.Messages.Message
| mvexpand ResponseMessages
| spath input=ResponseMessages
| eval Text = if(like(Text,"Transaction%"),"Transaction",Text)
| timechart count by Text
You should be able to group all the transaction with this query.
You can also add some parameters to the timechart function like that
| timechart limit=0 useother=false count BY Text, that should return you every error and not combine them under OTHER field.
Let me know if it works for you
KailA
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
We can try to group all the transaction into the same field so you don't have a column by Process Id ! 🙂
index=my_favorite_index "message.location"="cancelContract"
| spath input=message.data.responseBody output=ResponseMessages path=soap:Envelope.soap:Body.CancelContractResponse.CancelContractResult.Messages.Message
| mvexpand ResponseMessages
| spath input=ResponseMessages
| eval Text = if(like(Text,"Transaction%"),"Transaction",Text)
| timechart count by Text
You should be able to group all the transaction with this query.
You can also add some parameters to the timechart function like that
| timechart limit=0 useother=false count BY Text, that should return you every error and not combine them under OTHER field.
Let me know if it works for you
KailA
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I had to add the closing parenthesis for the like() function, then it worked great!