- Splunk Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Equals SIgn Not Being Handled For Searches
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
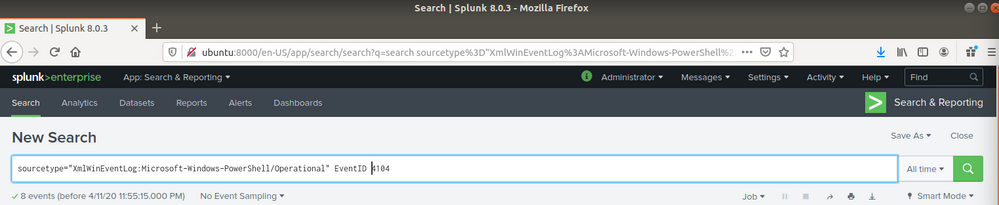
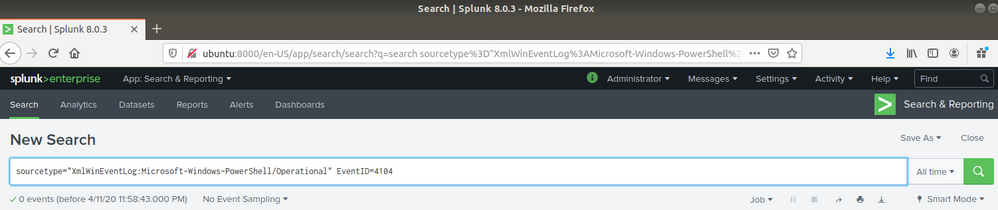
It looks like fields are not being extracted from the events. That's why the first search fails to find field 'EventID' with the value '4104', but the second search successfully finds events containing texts 'EventID' and '4104'.
Did you install a Windows TA after you wiped the server?
If this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It looks like fields are not being extracted from the events. That's why the first search fails to find field 'EventID' with the value '4104', but the second search successfully finds events containing texts 'EventID' and '4104'.
Did you install a Windows TA after you wiped the server?
If this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you for replying. I did install Windows TA after I removed everything referencing Splunk. I may uninstall and try to reinstall Splunk or fall back to an older version.