- Splunk Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Re: Does anyone have an explanation for the differ...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello,
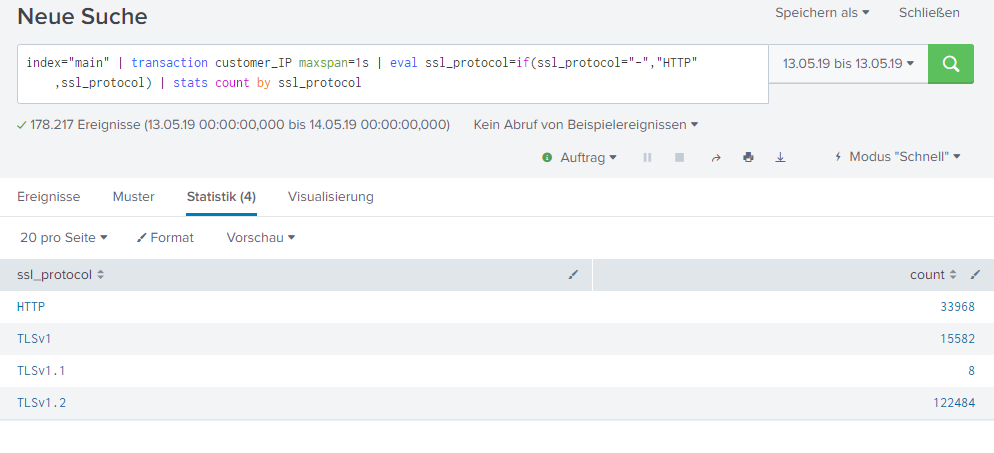
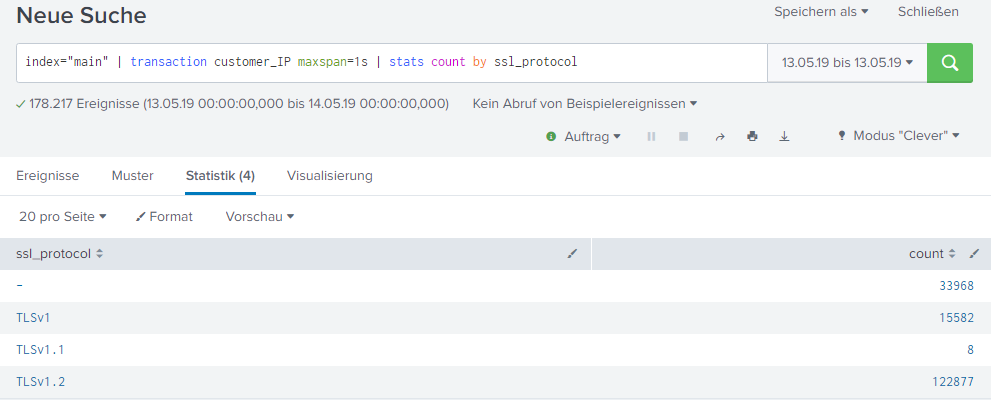
on searching for discrepancies in my dashboard I was able to cut down the problem to the following to searches. Maybe there is an explanation for it. The difference is in the count of TLSv1.2.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @gesa_behrens,
This is happening because a single transaction contains sometimes more than one ssl_protocol field values which means that if the condition matches on "-" everything gets replaced by the "HTTP" string.
You might want to run your eval before building the transaction then you'll be good on the count.
Cheers,
David
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @gesa_behrens,
This is happening because a single transaction contains sometimes more than one ssl_protocol field values which means that if the condition matches on "-" everything gets replaced by the "HTTP" string.
You might want to run your eval before building the transaction then you'll be good on the count.
Cheers,
David
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
wow, that was quick, and now that you mention it, this is absolutely clear to me, should have seen it my self.
Thanks so much!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
hahah most welcome 😉