- Splunk Answers
- :
- Using Splunk
- :
- Splunk Search
- :
- Can you help me with the where command?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I use the seatrch below
index="*" sourcetype="*"
| eval Boot_Duration=coalesce('Durée du démarrage ','Boot Duration ','Startdauer ','Duración del arranque ')
| dedup host
| stats count by host
Boot_Duration is a number value.
I want to check only the number values >100000
So I do
| where Boot_Duration>100000
But it doesn't work.
Could you help me please??
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Try:
index="" sourcetype=""
| eval Boot_Duration=coalesce('Durée du démarrage ','Boot Duration ','Startdauer ','Duración del arranque ')
| rex field=Boot_Duration (?P<Boot_Duration>^\d+)
| search Boot_Duration>=100000
| dedup host
| stats count by host
Your stats command 'looses' the Boot Duration field, so you either need to filter it before the stats, or bring the field through after your stats command has produced results
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You need to pass Boot_Duration through the stats so try using this instead:
| stats count, max(Boot_Duration) as Boot_Duration BY host
Or perhaps you would prefer avg() or min() over max().
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Try this (stop using dedup and surely your fields do not really have all of those spaces in them, do they?):
index="*" sourcetype="*"
| eval Boot_Duration=coalesce('Durée du démarrage',' Boot Duration', 'Startdauer', 'Duración del arranque')
| where Boot_Duration>100000
| stats count by host
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
thanks woodcok but i prefer to use the code of nickhillscpl because I need a regex in order to extract "ms" after the boot duration....
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
same problem...
and unfortunately there is the space in the fields...
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@jip31 can you paste here a couple of your events examples please ?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
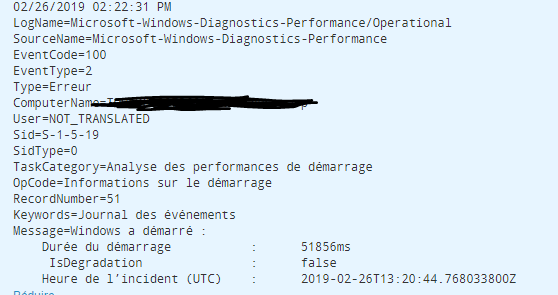
hi I have added the events in attachment
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@jip31
Can you please share sample events?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Try:
index="" sourcetype=""
| eval Boot_Duration=coalesce('Durée du démarrage ','Boot Duration ','Startdauer ','Duración del arranque ')
| rex field=Boot_Duration (?P<Boot_Duration>^\d+)
| search Boot_Duration>=100000
| dedup host
| stats count by host
Your stats command 'looses' the Boot Duration field, so you either need to filter it before the stats, or bring the field through after your stats command has produced results
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks a lot
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
responding to a comment above:
"wait - Boot_Duration includes 'ms' too?
This means its a string, not a number, and, you can't perform arithmetic logic on a string!"
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have edited the answer above to work if your duration field includes a unit of time (like 'ms')
This works by taking just the digits and stripping any letters from the field, so you can perform math comparisons on the field.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You mean that i have to do something like this :
| where Boot_Duration>100000. "ms" ???
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
No - try my example above.
In this case I am performing a regex on your Boot_Duration field - I read the entire field contents which I (now) assume contains something like "100929ms"
After the rex command, Boot_Duration will now only contain numbers ie "100929". Because this field is now numeric, you can perform <> operations on the values.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Use rex to extract only the number part of the field and then use Boot_Duration>1000
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You need to keep the boot duration on your stats command
| stats count, values(Boot_Duration) as Boot_Duration by host
Then you can your | where Boot_Duration>100000
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
tiago
it doesnt works
I think its because the boot duration has a value no?
for example : 100000ms
