- Splunk Answers
- :
- Splunk Premium Solutions
- :
- Security Premium Solutions
- :
- Splunk SOAR (f.k.a. Phantom)
- :
- How can I close a Notable from Phantom?
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I'm trying to close a Notable in ES from Phantom. I'm using the update event action from the Splunk app (v1.3.41) but it's failing when trying to validate my ES event_id.
That action validates the notable event ID by checking the incident review lookup. This lookup doesn't automatically have an entry for new notables - only when their status/comments/other is changed. The validation code in question - from splunk_connector.pyc - is as follows:
search_query = ('|`incident_review` | search rule_id={0}').format(ids)
ret_val = self._run_query(search_query, action_result)
if phantom.is_fail(ret_val):
return action_result.set_status(phantom.APP_ERROR, ('Error occurred while validating the provided event ID. Error: {0}').format(action_result.get_message()))
if int(action_result.get_data_size()) <= 0:
return action_result.set_status(phantom.APP_ERROR, 'Please provide a valid event ID')
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
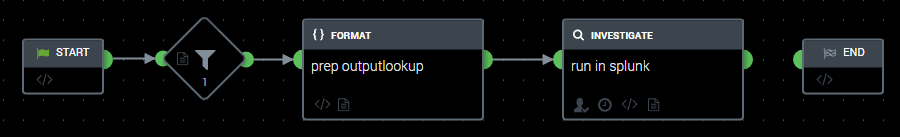
We're working around this by using a Close Notable playbook that submits the following 'query' to Splunk:
| eval event_id="{0}"
| eval _key=event_id, rule_id=event_id, comment="Closing from Phantom", time=now(), status=5, user="admin"
| table _key comment rule_id time status rule_name user
| outputlookup append=true incident_review_lookupWhere {0} is filtered-data:filter_1:condition_1:artifact:*.cef.event_id and the filter is just locating the artifact with the event_id.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We're working around this by using a Close Notable playbook that submits the following 'query' to Splunk:
| eval event_id="{0}"
| eval _key=event_id, rule_id=event_id, comment="Closing from Phantom", time=now(), status=5, user="admin"
| table _key comment rule_id time status rule_name user
| outputlookup append=true incident_review_lookupWhere {0} is filtered-data:filter_1:condition_1:artifact:*.cef.event_id and the filter is just locating the artifact with the event_id.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
There are much simpler and effective ways to do this. Assuming you have ES.
- Set up your asset configuration for splunk to point to ES .
- You can send an event through either an automated action inside a saved search, phantom app with a saved search forwarding a specific event to an active playbook or even a adaptive response action.
- All you need is to pass the ES Notable Event ID, Status and Integer and you should be able to do so.
The search provided does the job but here are other options worth considering.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi mzambrana123,
Thanks for the candid feedback, but I'm not sure you've understood the question correctly.
The problem isn't sending a Notable to Phantom, it's using Phantom to tell ES the Notable should be closed. If you're using latest version of the Splunk app within Phantom (1.3.41 at the time of writing) the action to update a status is broken as it assumes that notables will have an entry in the Incident Review lookup, which isn't true until someone makes a change to the case in ES i.e. assigns it to an analyst, changes, the status, leaves a comment etc.