- Splunk Answers
- :
- Splunk Platform Products
- :
- Splunk Enterprise
- :
- Splunk and Kaspersky Security Center 10
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Splunk and Kaspersky Security Center 10
I'm using Splunk Light and Kaspersky Security Center 10. Currently I have splunk monitoring and receiving syslogs, port 514, from many systems.
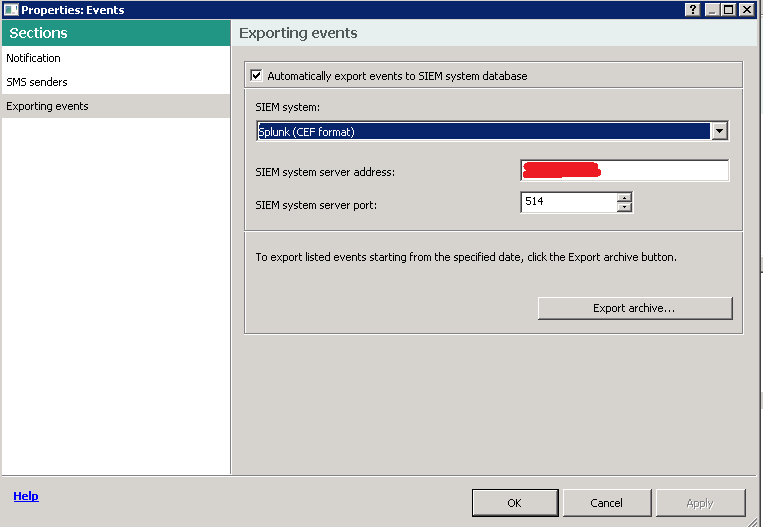
In KSC10 there is an option show in the image, to export CEF logs straight to Splunk. I set this and picked port 514. The host is not showing up in Splunk. I'm hoping someone can get me pointed in the right direction. I do know events are happening and I also tried to export the archive just to get the data moving.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi. It's 2018 and I'm having this problem.
I've configured everything per "https://support.kaspersky.com/9284" and set everything accoringly on my Splunk instance per this thread.
I've opened up the host firewall and network firewall, confirmed via netcat on KSC10 server that the TCP connection to the specified Splunk server remote port is opened, but I'm not seeing any logs in Splunk.
What am I missing?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Configuring the SIEM system on KSC10 is not enough! You need to configure the events you want to forward :
1. Open your polic[y|ies] and go to "Event Configuration" ;
2. On each Tab (Critical Event, Functional failure, Warning, Info), highlight each event you would like to have forwarded and click on the bottom right button "Properties" ;
3. On each event's Properties window, check the box "Export to SIEM system via syslog" and click OK;
4. Click OK once more to leave/update the policy.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I've built an add-on to parse kaspersky data in splunk but I used LEEF (Qradar) because when I started there was not splunk option. Its available in Splunkbase. In case you want to lend a hand so I can build the CEF part it would be great to have some CEF example data to work with.
Hope I was able to help you. If so, some karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
In Splunk, go to settings->data inputs, then click udp. Add a UDP port there if there is not already one (I used 50000 to be sure that there were no conflicts), then click next. On the next page, for sourcetype select operating system->syslog. Everything else can be the defaults, but I had the Kaspersky stuff go into it's own index, but that's just me.
In Kaspersky, go to the Administration Server page, and click "Configure Notifications and Event Export", then select "Configure export to SIEM system." Make sure that "automatically export..." is checked, select "Splunk (CEF Format)" for the SIEM system, enter the IP address of your Splunk server, enter the port that you selected in Splunk and UDP. Click apply.
Data should start showing up in Splunk now.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Do I need add-on for data from kaspersky security center?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes, you should send data from Kaspersky Security Center. For me didn't worked because of the license. Apparently to send logs to an external syslog you need an extra license from Kaspersky .
PS: You can send the log as well with an universal forwarder.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello Marcmuher,
the log received from Kaspersky to Splunk are coming already parsed?
Thanks
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
is there anyone to help ?,it happend to me,is there any one that can hel us to solve this problem ?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello, someone have any update about this issue?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
same thing here, there is no way to get this info in the raw logs.
I've configured my inputs.conf with a predefined host name.
Did you ask Kaspersky support?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have not. Since kaspserky has it build in, with a drop down for splunk, a port, and a server IP, I figured it sends them like syslog does... there's not much to mess up here. I was hoping it's something that needs setup on the splunk side to get this going.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I check with local teams and they do not have sufficient knowledge and setup to demonstrate the working model.
I am trying but running out of Kaspersky trial license limit. If you are still interested, I can invest to rebuild another AWS instance to try it out.