- Splunk Answers
- :
- Splunk Administration
- :
- Security
- :
- What would be the recommended Log Levels for the d...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
What would be the recommended Log Levels for the different Audit Log channels?
Hi All,
This is more a general inquiry
I noticed that the _audit index collects a lot of activity, but it's not really telling in detail what actually has been done (if anything at all) .. edit user / edit role / edit index / remove ...
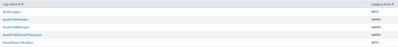
What would be the recommended Log Levels for the different Audit Log channels?
If I would like to see in details what has been changed for a certain index, what Log channel(s) and what Log Level(s) would result in showing that information?
Note, that in our environment any changes to indexes are done in the (Linux) server directly, not using the UI
Thanks in advance!
Edwin
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Splunk audit log is known to be weak in some respects and I don't know that changing the log level will help.
Changes made outside the UI (or REST API) do not appear in the audit log that won't help you track changes to the indexes.
Consider upgrading to Splunk 9.x and enabling the Configuration Tracker. It will log changes to pretty much any .conf file and log them to the _configtracker index. Unfortunately, even Config Tracker does not specify which person made the change.
If this reply helps you, Karma would be appreciated.