- Splunk Answers
- :
- Using Splunk
- :
- Reporting
- :
- Report of Clients
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Report of Clients
Hello,
How can I create a list of All clients reporting into a host, whether matched or unmatched?
This should be a very simple task, but I sure cannot find a solution.
Thanks,
Terry
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi
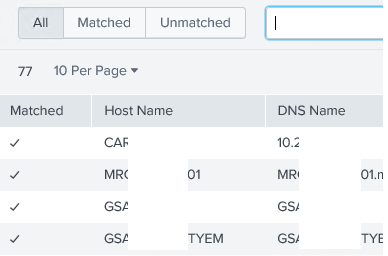
another option is enable forwarder monitoring on your MC (or your local instance).
Settings -> Monitoring Console
-> Settings -> Forwarder Monitoring Setup
Then wait some time and look with
Settings -> Monitoring Console
-> Forwarders -> Forwarders: Deployment
r. Ismo
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
No errors, but no results either.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @teeeebro,
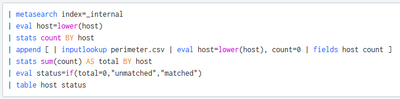
sorry, my error: I forgot thet you don't have events but csv rows!
Please this this (the same thing without metasearch and rename the hostname field):
if the hostname in csv is called "Hostname" (otherwise rename it!):
index=your_index
| eval Hostname=lower(Hostname)
| stats count BY Hostname
| append [ | inputlookup perimeter.csv | eval Hostname=lower(host), count=0 | fields Hostname count ]
| stats sum(count) AS total BY Hostname
| eval status=if(total=0,"unmatched","matched")
| table Hostname statusThe logic is:
- you have a list of hosts with rows in csv in "count" field,
- you add the lookup's list of hosts each one with count=0,
- you sume the count field from inde and lookup.
So:
- total=0 means that you have only the host in the lookup,
- total>0 means that you have the host both in index and lookup.
Ciao.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
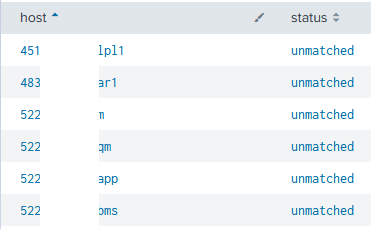
It was user error on my part. I have results now, however, they are ALL unmatched.
In the CSV I list all 1035 of our servers. The end result I'm looking for is a list of all systems Splunk sees, whether matched or unmatched.
We are just getting started with deploying the agent to our 1035 servers, and I need a CSV export so I can reconcile any differences. If I have a list of all 1035 servers, and a list of what Splunk sees, it takes 30 seconds for Excel to do a column comparison.
Hope that makes sense. And THANKS for the help! I am Way further ahead now that I was earlier.
Regards,
Terry
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @teeeebro,
at first check if the matched are at the end of the list.
if you have all unmatched means that you can read from the lookup but not from the index
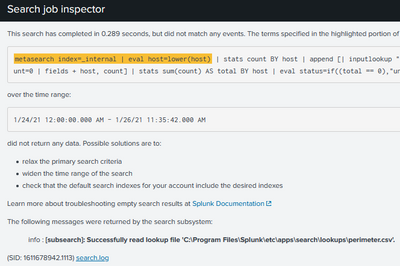
what happens if you run:
| metasearch index=_internal
| eval host=lower(host)
| stats count BY host?
Ciao.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes - I need a little more guidance, please.
I created the CSV which contains a list of ALL my server hostnames. The search read the file, but there are no results.
This was my search
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @teeeebro,
the lookup is called "perimeter.cav", contains at least a column called "host", you creted it and you created also the related lookup definition for this lookup, is it correct?
then, what do you mean with "no results"?
at least you should have the hosts from lookuop and the hosts from _internal, which resuld have you?
Ciao.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @teeeebro,
are you speaking of servers monitored by Splunk Universal Forwarders?
If this is you need, you have to create a list (in a lookup called e.g. perimeter.csv) containing all the clients to monitor (at least one column called e.g. host) and then run a search like this:
| metasearch index=_internal
| eval host=lower(host)
| stats count BY host
| append [ | inputlookup perimeter.csv | eval host=lower(host), count=0 | fields host count ]
| stats sum(count) AS total BY host
| eval status=if(total=0,"unmatched","matched")
| table host statusCiao.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you for the reply.
Yes - I need a list of servers monitored by Splunk Universal Forwarders.
I'm very new to using Splunk, but I'll take what you provided and give it a shot.
Thanks again!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @teeeebro,
tell me if you solve or if you need more help.
Ciao and happy splunking.
Giuseppe
P.S.: karma Points are appreciated 😉