- Splunk Answers
- :
- Using Splunk
- :
- Reporting
- :
- How can I remove a "tag=error" that mysteriously s...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have no idea how this happened, but one of my savedsearches broke today and it turns out its because my source file was tagged as "error".
I cannot get rid of it and I can't find my tags.conf file in my \local folder. This source folder is actually set as two tags which is also weird.
More info is that this is affecting more than 18 sources and 100K records.
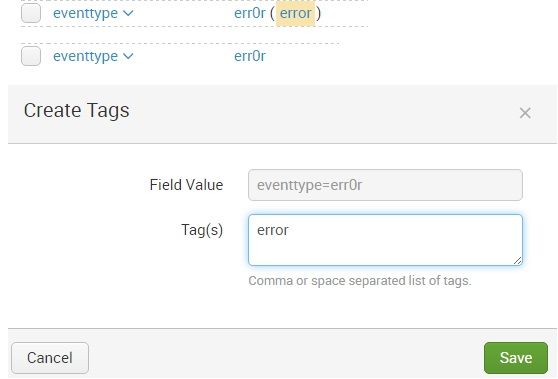
Somehow my tag::eventtype was set to error for all but one of these issues. I've never used tag::eventtype. I think my index may be messed up.
Should I blow away the index and start over? I don't really want to do that.
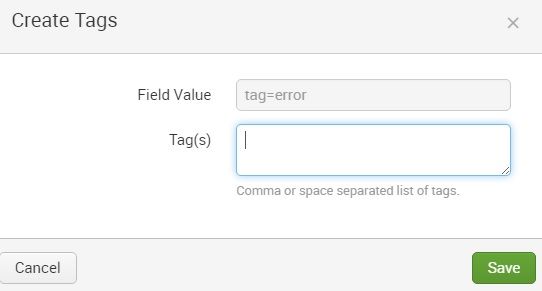
Update: I've deleted the tag::Eventtype but it keeps coming back. This is what the tag::eventtype looks like.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi jgpm!
One of the main selling features of splunk is it's schema on the fly, allowing for the creation of knowledge objects like tags and eventtypes at searchtime! Blowing away your index is only really necessary in certain cases, and I am confident this won't be one of them.
The reason it likely popped up out of nowhere, is that an app or TA was installed.
This eventtype is part of the Splunk CIM app. Can you confirm you have this installed? check $SPLUNK_HOME/etc/apps and let us know so we can help you track down the config!
EDIT: updated answer to point future reader to CIM app
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi jgpm!
One of the main selling features of splunk is it's schema on the fly, allowing for the creation of knowledge objects like tags and eventtypes at searchtime! Blowing away your index is only really necessary in certain cases, and I am confident this won't be one of them.
The reason it likely popped up out of nowhere, is that an app or TA was installed.
This eventtype is part of the Splunk CIM app. Can you confirm you have this installed? check $SPLUNK_HOME/etc/apps and let us know so we can help you track down the config!
EDIT: updated answer to point future reader to CIM app
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
so you've gone into your event types and deleted the event type called 'err0r'?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
So I freaked out a bit early. I did check eventtypes last night and it was empty...but I had to unfilter a few things and I found it and disabled it. It was related to the CIM app which I had installed yesterday as well. I apologize for the unnecessary post.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Don't be sorry! It's a great and necessary learning experience! the post will likely help people in the future!
Glad to see you got it sorted!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Helped me... Thx!