- Splunk Answers
- :
- Splunk Administration
- :
- Getting Data In
- :
- Re: Why is the TIMESTAMP_FIELDS setting in props.c...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I have the issue that the TIMESTAMP_FIELDS setting in the props.conf on the Universal Forwarder is not taken into account. It seems like the field _time is filled in with the time the line is being indexed and not take from the log line itself.
Splunk Enterprise:
VERSION=6.6.3
BUILD=e21ee54bc796
PRODUCT=splunk
PLATFORM=Linux-x86_64
Splunk Universal Forwarder:
VERSION=6.6.3
BUILD=e21ee54bc796
PRODUCT=splunk
PLATFORM=Linux-x86_64
Log line example:
{"Application":"CNIP","CallStatus":"OK","CallType":"TERM-RP","Called":"xxxxxxxxx","Calling":"xxxxxxxxx","Clir":"false","DelayTime":"161","Error":"","ErrorBy":"","ErrorSeverity":"","Name":"xxxxxxxxx","NameBy":"DisDB","OverwriteCli":"","Protocol":"SIPPROXY","SessionId":"xxxxxxxxx","StartTime":"2018-06-20T08:36:00Z","StopTime":"2018-06-20T08:36:00Z","logLevel":1}
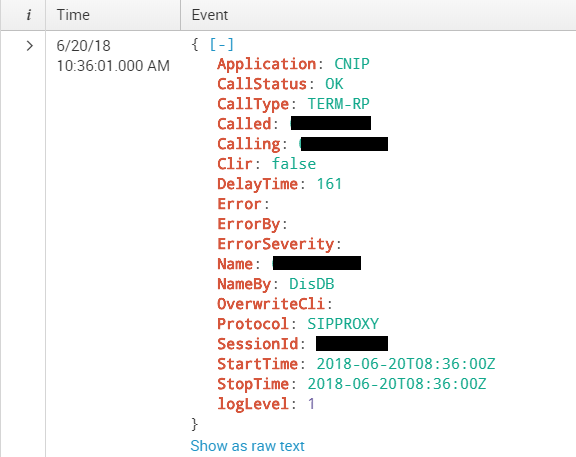
How it is seen on Splunk:
As you can see, the times are not taken from the "StartTime" field in the logline.
Here the config on the Forwarder:
inputs.conf
[monitor:///locationOnServer/LogFile]
index=csdp_prod_services
source=CNIPService
sourcetype=CnipCallLog.log
ignoreOlderThan=1d
props.conf
[CNIPService]
SHOULD_LINEMERGE=false
INDEXED_EXTRACTIONS=json
KV_MODE=none
category=Structured
disabled=false
TIMESTAMP_FIELDS=StartTime
TZ = UTC #I tried with and without this field, same behavior
TIME_FORMAT=%FT%TZ #I tried with and without this field, same behavior
What am I missing here to make this work? I want the _time field to be filled in based on the "StartTime" field in the log lines.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Problem is solved.
What I did was a combination of the answers above.
I added the following to the props.conf on the indexer (so not the UF):
TIME_PREFIX = StartTime\":
TIME_FORMAT=%FT%TZ
TIME_PREFIX: The \" after the field name (as proposed above) was not needed, this caused the indexer to stop accepting new events on this input.)
After applying these changes, it worked perfectly!
Thank you all for the help!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Problem is solved.
What I did was a combination of the answers above.
I added the following to the props.conf on the indexer (so not the UF):
TIME_PREFIX = StartTime\":
TIME_FORMAT=%FT%TZ
TIME_PREFIX: The \" after the field name (as proposed above) was not needed, this caused the indexer to stop accepting new events on this input.)
After applying these changes, it worked perfectly!
Thank you all for the help!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Shouldn't that props.conf go on your indexer instead of the UF?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
When I add the following config to the indexer instead of the UF:
TIME_PREFIX = StartTime:
TIME_FORMAT=%FT%TZ
--> same behavior so not working.
When I add the following config to the indexer instead of the UF:
TIME_PREFIX = StartTime\":\"
TIME_FORMAT=%FT%TZ
--> nothing is being indexed anymore for this input.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Can you try TIME_PREFIX = StartTime: instead of TIMESTAMP_FIELDS?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
It should be TIME_PREFIX = StartTime\":\"
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
That is also not working.
just now, I did notice that if I change the language (change en-Us to en-GB in the url), the display of the timestamp is not changing on Splunk. So could this be a clue? Splunk seems not to recognize the timestamp format.
On other log we have (with different timestamp formats) we do see the display of the timestamp changing when changing the language of the web GUI.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This proposal has the same behavior. So it is still not working.