- Splunk Answers
- :
- Splunk Administration
- :
- Getting Data In
- :
- Parsing McAfee Firewall Logs
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hello All!
I am trying to parse McAfee firewall logs but the props.conf I am using doesn't seem to work.
This is my props.conf:
[source::<source location>]
TIME_PREFIX = Time:\s+
TIME_FORMAT = %m/%d/%Y %H:%M:%S
LINE_BREAKER = ([\r\n]+)Time:
SHOULD_LINEMERGE = false
This is the log that I want to break at each timestamp line:
Time: 03/04/2021 17:31:18
Event: Traffic
IP Address: 172.16.0.21
Description:
Path:
Message: Blocked Incoming UDP - Source 172.16.0.21 : (54915) Destination 172.16.0.255 : (54915)
Matched Rule: Block all traffic
Time: 03/04/2021 17:31:19
Event: Traffic
IP Address: 172.16.0.21
Description:
Path:
Message: Blocked Incoming UDP - Source 172.16.0.21 : (54915) Destination 172.16.0.255 : (54915)
Matched Rule: Block all traffic
Time: 03/04/2021 17:31:20
Event: Traffic
IP Address: 172.16.0.21
Description:
Path:
Message: Blocked Incoming UDP - Source 172.16.0.21 : (54915) Destination 172.16.0.255 : (54915)
Matched Rule: Block all traffic
Time: 03/04/2021 17:31:21
Event: Traffic
IP Address: 172.16.0.21
Description:
Path:
Message: Blocked Incoming UDP - Source 172.16.0.21 : (54915) Destination 172.16.0.255 : (54915)
Matched Rule: Block all traffic
Time: 03/04/2021 17:31:22
Event: Traffic
IP Address: 172.16.0.21
Description:
Path:
Message: Blocked Incoming UDP - Source 172.16.0.21 : (54915) Destination 172.16.0.255 : (54915)
Matched Rule: Block all traffic
...
Thank you so much!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
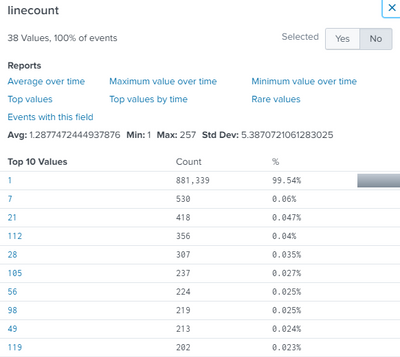
Just figured it out, instead of using source, sourcetype should be used in the props.conf. Now I am seeing proper events break-up:
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
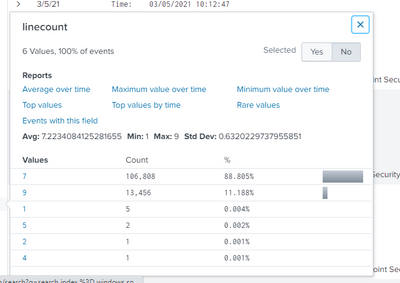
From my perspective your props.conf looks good. Are your events currently being indexed line by line?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yeah, the vast majority are 1 line, and there are many other line counts. What I need is events with 7 lines. BTW, the props.conf is on heavy forwarders to send to Splunk Cloud.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Just figured it out, instead of using source, sourcetype should be used in the props.conf. Now I am seeing proper events break-up: