Join the Conversation
- Find Answers
- :
- Splunk Administration
- :
- Getting Data In
- :
- Collecting Windows eventlogs with whitelist based ...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Collecting Windows eventlogs with whitelist based on word
Hi
I need to collect all Windows security logs from my infrastructure with Splunk UF installed which include specific Keyword
I'm using following config for Splunk add-on for Windows, but this results in collecting all logs from server.
[WinEventLog://Security]
disabled = 0
start_from = oldest
current_only = 0
checkpointInterval = 5
whitelist1 = (?msi)^Workstation\s+Name\:\s+KEYWORD
index = wineventlog
renderXml=false
How can I do this correctly?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You should be able to do it provided you have the event field name.
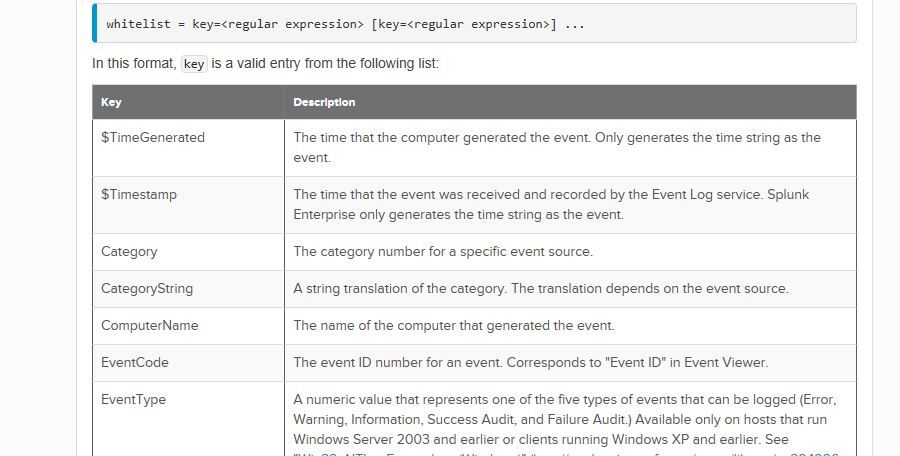
The syntax is -
whilelist = <list> | key=regex [key=regex]
You have so far -
whitelist1 = (?msi)^Workstation\s+Name\:\s+KEYWORD
Based on the doc you provided at Monitor Windows event log data
you need to identify the key -
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes in this way you take all security eventlogs.
if you want not all logs but only the ones that contain specific words, you have to filter them using props.conf and transforms.conf on your indexer.
Bye.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes, this is traditional way for doing this, but it impacts performance of indexers.
As I found in docs (http://docs.splunk.com/Documentation/Splunk/6.4.2/Data/MonitorWindowseventlogdata) I have ability to filter some logs on UF side and filter could be based on regex.
So my question is what am I doing wrong in my example and how to make it working?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
For my Splunk knowledge, Universal Forwarders don't parse logs, parsing is done by Heavy Forwarders and Indexers.
There are two ways to don't parse logs on the Indexer:
- put an Heavy Forwarder between Universal Forwarders and Indexer and use it to filter logs,
- get logs not directly from wineventlog but from a script that runs on the Universal Forwarder and writes the filtered logs in a file.
Bye.
Giuseppe