- Splunk Answers
- :
- Using Splunk
- :
- Splunk Dev
- :
- Re: Reconfiguring timestamp to match csv row, not ...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
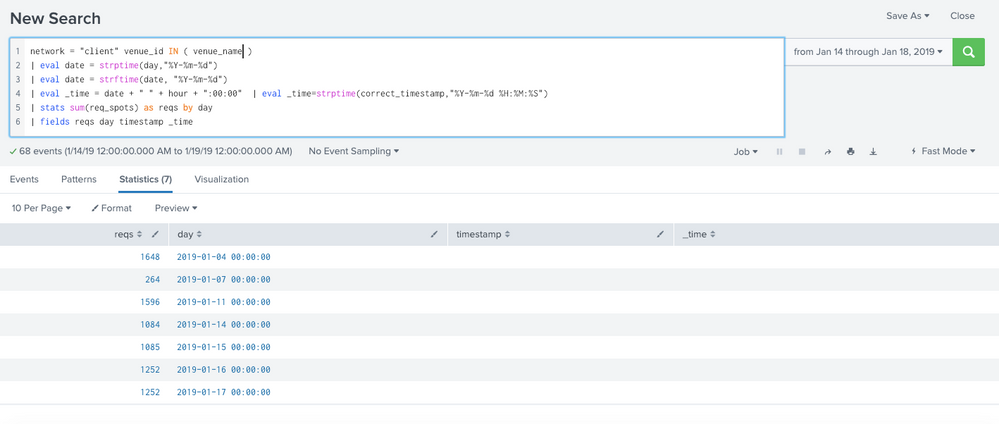
Reconfiguring timestamp to match csv row, not indexing time
Hi! I am attaching a screenshot of my query as the problem is immediately apparent. I am searching only for dates 1/14-1/18. I have data in Splunk that has a "day" and "hour" column, and I want that to be the source of truth for my dates. I think Splunk is ignoring them and setting a timestamp based on time of index. Can you please tell me how to troubleshoot configuring the timestamp? As you can see, I am trying to display _time or timestamp but these are not even selected fields. How do I make my query only contain the dates within my selected range (excluding 1/04, 1/07, etc.)
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
you could instead of day use _time and get the actual date from _time.
eval date = strftime(_time,"%Y-%m-%d")
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sorry, not sure I understand your suggestion. You can see that _time is empty in my table, so using that field returns no results. "day" is a column header in my data which has the timestamp I want to use, so I definitely want that field included in my query.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
_time by default is never empty it always has timestamps. In your table it is empty because you are using stats by day and not by _time. The result of your stats is table with reqs and day field. So you cannot see _time field as its already removed by stats command
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Even if I use _time, it is still returning results from the days outside of my selected time range. How do I make the time range apply to the dates that I want? I have it now so that eval _time is returning the correct dates, but the results are still being returned are still all of the ones indexed during those dates.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The time range looks time from _time , so if you select time from 14th jan to 18th jan, it will pick time from _time from that range only. Try below search
network="client" venue_id IN(venue_name)| bin span=1d _time| stats sum(req_spots) as req by _time| fields _time reqs
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Sorry, but as I explained this will not work. This query groups all the requests between 1/04-1/15 into the 1/15 timestamp. This is because all of this data was indexed on 1/15. I do not want the _time to look at when the data was indexed. I want it to look at the timestamp within the csv.