Are you a member of the Splunk Community?
- Find Answers
- :
- Using Splunk
- :
- Dashboards & Visualizations
- :
- Re: How to get the total count of events for earli...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I am trying to get the total count of a field called ID for earliest and latest time for a particular time range. Assume I am looking for a time range of Mor 8AM to 5PM . I want the count of total for a field called "ID" for 8AM TO 9AM and also count from 4PM TO 5PM for field called 'ID" and show what is different if there is a difference in values of ID for hours 8AM TO 9AM and 4PM TO 5PM .
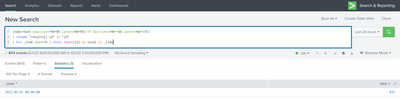
Following is the query I am using
index=test
| rename "results{}.id" as "id"
| bin _time span=1h | stats count(id) as total by _time
| delta total as difference
| fillnull value=0
|eval status=case(difference=0, "No change", difference<0, "Device(s) Removed" , difference>0 ,"Device(s) Added")
| search status!="No change"
| rename _time as time | eval time=strftime(time,"%m/%d/%y %H:%M:%S")
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Try something like this
index=test (earliest=@d+8h latest=@d+9h) OR (earliest=@d+16h latest=@d+17h)
| rename "results{}.id" as "id"
| bin _time span=1h | stats count(id) as total by _time
| delta total as difference
| fillnull value=0
|eval status=case(difference=0, "No change", difference<0, "Device(s) Removed" , difference>0 ,"Device(s) Added")
| search status!="No change"
| rename _time as time | eval time=strftime(time,"%m/%d/%y %H:%M:%S")- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Try something like this
index=test (earliest=@d+8h latest=@d+9h) OR (earliest=@d+16h latest=@d+17h)
| rename "results{}.id" as "id"
| bin _time span=1h | stats count(id) as total by _time
| delta total as difference
| fillnull value=0
|eval status=case(difference=0, "No change", difference<0, "Device(s) Removed" , difference>0 ,"Device(s) Added")
| search status!="No change"
| rename _time as time | eval time=strftime(time,"%m/%d/%y %H:%M:%S")- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you it worked.I never know that we can add + in earliest and latest.Thank you I learned something new
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I tried to run line by line. I ran the below search but I only got 8AM events.
index=test (earliest=@d+8h latest=@d+9h) OR (earliest=@d+16h latest=@d+17h)
| rename "results{}.id" as "id"
| bin _time span=1h | stats count(id) as total by _time
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
What time did you run it at? The time selection is based on today - if you want yesterday for example use
index=test (earliest=-1d@d+8h latest=-1d@d+9h) OR (earliest=-1d@d+16h latest=-1d@d+17h)
| rename "results{}.id" as "id"
| bin _time span=1h | stats count(id) as total by _time