- Splunk Answers
- :
- Using Splunk
- :
- Alerting
- :
- How to collect specific data from global list and ...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
How to collect specific data from global list and alert anomalies? Transactions analysis
Hi everybody!
I know that my question could sounds primitive for senior Splunkers but I don't have other way to get needed knowledge.
I have to make transaction analysis mechanism in my company which can be able to catch and alert every anomaly in transaction value - it will be the first indicator of fraud.
At first I'll describe the structure of data what I have.
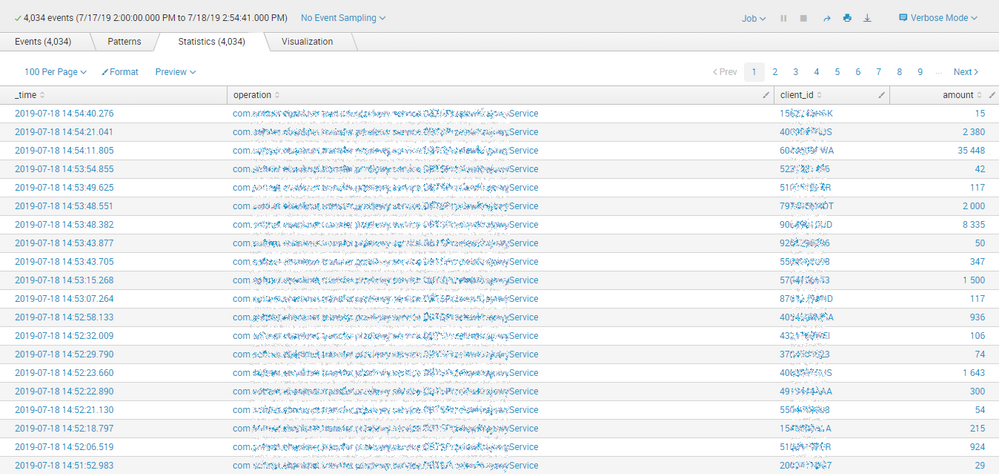
As you see there is four data fields. Operation timestamp, operation name, username and amount of transaction. It's enough data for this level of analysis.
What I want to do is to collect transaction value for each client from this table and then using this values to calculate "normal" value for each client_id.
Let's assume that model of "normal" value is just average value for each client_id.
I want to be alerted in every case when this "normal" value for each client_id will be exceeded in new event.
It's the simplest antifraud mechanism ever but enough for our scale of working. I don't have idea how to do it well. Can You help me and tell which commands, functions and syntax I need to interest of to do it? I'll be pleased for every little answer from You.
I'm begginer Splunk user but I hope someday I also could answer here for other begginers question. 🙂
Have a nice day and answer please!
KF