- Apps and Add-ons
- :
- All Apps and Add-ons
- :
- Re: eNcore eStreamer 3.6.1 fieldalias not being ap...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
eNcore eStreamer 3.6.1 fieldalias not being applied
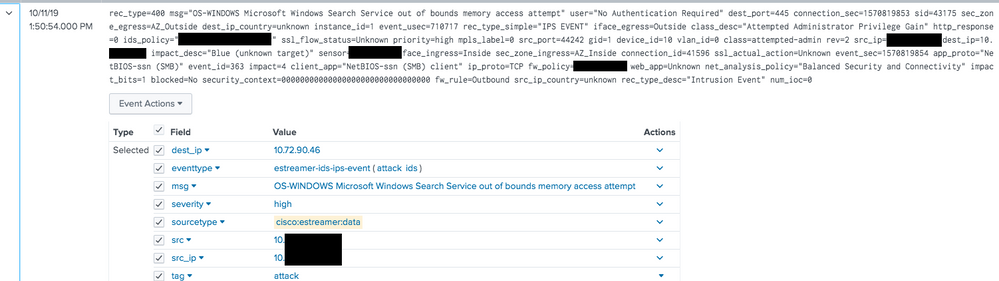
Deploying eNcore eStreamer 3.6.1 I have found that the field alias for intrusion signatures is not being applied in my searches:
./splunk cmd btool props list cisco:estreamer:data | grep ALIAS
...
FIELDALIAS-estreamer_intrusion_signature = msg AS signature
FIELDALIAS-estreamer_severity = priority AS severity
FIELDALIAS-estreamer_src = src_ip AS src
Attached is a screenshot for one event, you can see that src and severity are there, but there is no signature. Without the fieldalias, anything in the Intrusion Data Model has unknown for the signature of the attack in it.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I got the same issue but with eStreamer 4.2 and 4.0. If you are using Splunk 7.2 or later, there is a limitation you can't use two field aliases for the same field. Take a look into signature aliase:
cisco:estreamer:data : FIELDALIAS-estreamer_intrusion_signature
cisco:estreamer:data : FIELDALIAS-estreamer_malware_signature
You need to remove the overwrite on both Field Aliases.
Regards,
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks for the update. I'll review with our developer.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Actually I believe I have fixed the issue I'm having (signature aliases for both malware and intrusion detection data models).
I've removed the FIELDALIASES that try and create the fields required, and replace it with my own in local directory...
props.conf
[cisco:estreamer:data]
EVAL-signature = coalesce(msg,detection)
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
we've more recently pushed 3.6.8 with more bug fixes.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This doesn't have seem to fix the field aliases.. I'm having the EXACT same problem, only seems to be having issues with signature for intrusion detection data model.
Splunk version: 7.2.6
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
3.6.1 has a bug that we discovered on 10/11. We changed default download to 3.5.8. There will be a 3.6.x posted in a few days that will fix the issue.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@douglashurd Does the 3.6.x fixed version also include the missing eventtypes and tags that I mentioned in this question?