- Apps and Add-ons
- :
- All Apps and Add-ons
- :
- Unclear checkbox in Splunk Security Essentials
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Unclear checkbox in Splunk Security Essentials
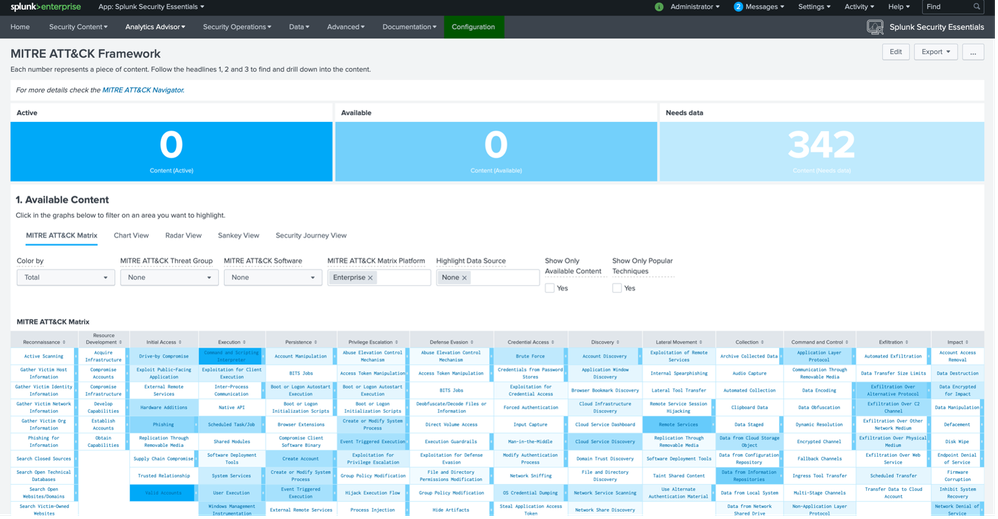
In Mitre ATT&CK Framework's dashboard of Splunk Security Essentials app there is an unclear checkbox: the label sais "Show Only Available Content" and the tooltip sais: "This checkbox filters out the MITRE ATT&CK Techniques that do not have an associated detection in this Splunk environment, i.e. it removes all cells with zeros."
This checkbox is not filtering on data showing only the Available Detections or removing cells with all zeros for Active, Available and Needs Data. This checkbox filters data showing only the TTPs with a note technique or detectable in actual environment.
The actual state is:
In this picture you can see the filter working: the cells with “Active”, “Available” and “Needs Data” with all zeroes are still displayed.
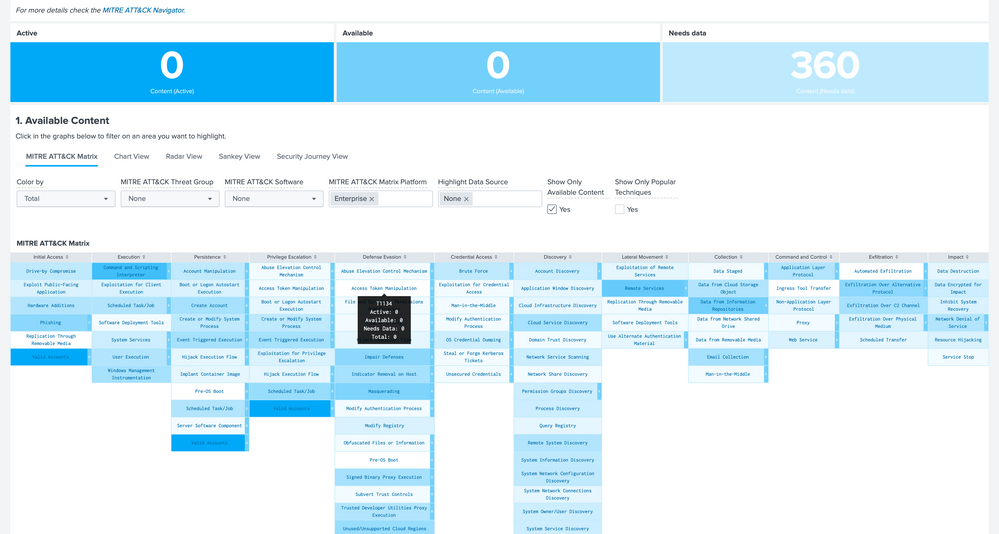
We just improved the dashboard by changing the label on the first checkbox and introducing 3 new checkboxes:
- Show only active detections
- Show only available detections
- Show only needs data detections
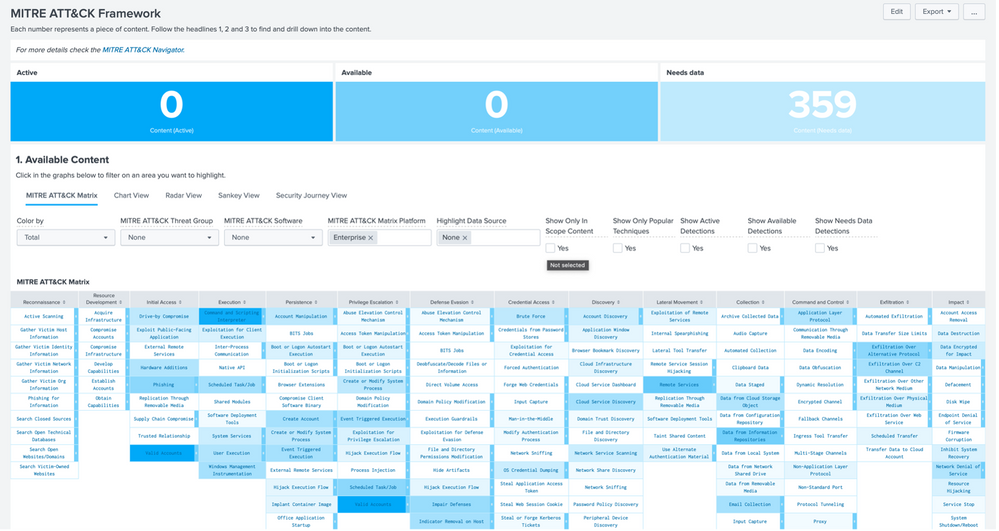
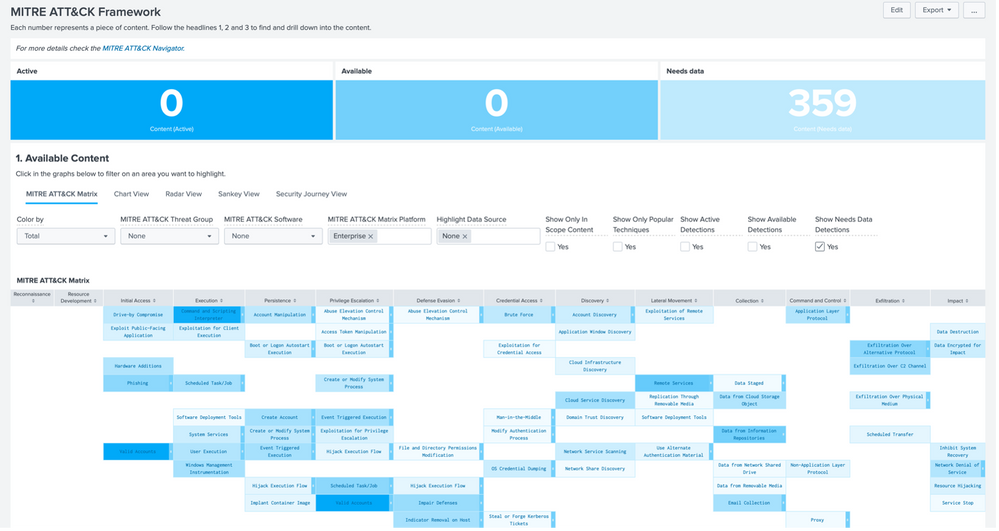
This is the dashboard with new checkboxes:
This is how the filter works: only cells with "Needs Data" parameter != 0 are displayed in matrix.
For achieving this we have edited this files:
- mitre_overview.xml: dashboard file to edit checkbox, labels and panel search
- advisor_analytics.js: to edit tooltips' text
The checkboxes are built in this way:
<input type="checkbox" token="active_content_token" searchWhenChanged="true">
<label>Show Active Detections</label>
<choice value="'Active'>0">Yes</choice>
<default>0=0</default>
<delimiter> </delimiter>
</input>
If the box is checked the value of “yes” is <fieldname>>0, default value is an always true clause. In this picture is displayed the checkbox used for selecting only the "Active" rules. So the value is 'Active'>0 and the default is 0=0.
The search in matrix panel is changed in the last three evals:
...
| eval "<<FIELD>>" = if(text!="" AND $needs_data_token$ AND $active_content_token$ AND $available_content_token$,mvappend("TechniqueId: ".'<<FIELD>>_TechniqueId',"Technique: ".Technique,"Color: ".color,"Opacity: ".opacity,"Active: ".p0_count,"Available: ".p1_count,"Needs data: ".p2_count,"Total: ".total_count,"Selected: ".p3_count,"Groups: ".'<<FIELD>>_Groups'),null)
| eval "<<FIELD>>"="{".mvjoin(mvmap('<<FIELD>>',"\"".mvindex(split('<<FIELD>>',": "),0)."\": \"".mvindex(split('<<FIELD>>',": "),1)."\""),",").Selected_Threat_GroupsJson.Selected_SoftwareJson.",".Software_Json.Sub_Technique."}"
| eval count = count + 1
...
The js file is changed only for display appropriate text in labels, this are the changes:
/**
* The below defines tooltips.
*/
require(["jquery",
"splunkjs/ready!",
"bootstrap.popover",
"bootstrap.tooltip"
],
function(
$, Ready) {
/* edited rules */
$("label:contains('Show Active Detections')").prop('title', 'Filters TTPs showing only the active rules');
$("label:contains('Show Available Detections')").prop('title', 'Filters TTPs showing rules available but not active');
$("label:contains('Show Needs Data Content')").prop('title', 'Filters TTPs showing rules that need data to work');
$("label:contains('Show Only In Scope Content')").prop('title', 'This checkbox filters out the MITRE ATT&CK Techniques that do not have a defined technique for detection or a defined rule for detection in this Splunk environment.');
We ask to introduce this improvements with the next update, if needed we can provide files with changes.