- Apps and Add-ons
- :
- All Apps and Add-ons
- :
- Re: Configure multiple accounts using assume role ...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Configure multiple accounts using assume role policy?
I have been using the documentation, but AWS user permissions, groups and policies are confusing enough, to add the documentation doesn't seem very clear to me.
So on my event collector where I do all the configurations, I have the autodiscovered ec2 role for the eventcollector machine configured so it can access information in that account for the AWS app. I want to add more AWS accounts and have been following this page. http://docs.splunk.com/Documentation/AddOns/released/AWS/ConfigureAWSpermissions
It states "If the user is in a different account than the role, then the user's administrator must attach a policy that allows the user to call AssumeRole on the ARN of the role in the other account."
So if account A is the account that is working with the ec2 role tied to the event collector, do I create a user on account B and set
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Action": "sts:AssumeRole",
"Resource": "arn:aws:iam::ACCOUNTA:role/eventcollector"
}
]
}
Then on the A Account set the role to
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "",
"Effect": "Allow",
"Principal": {
"AWS": "arn:aws:iam::ACCOUNTB:user/splunkcollectinguser"
},
"Action": "sts:AssumeRole"
}
]
}
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
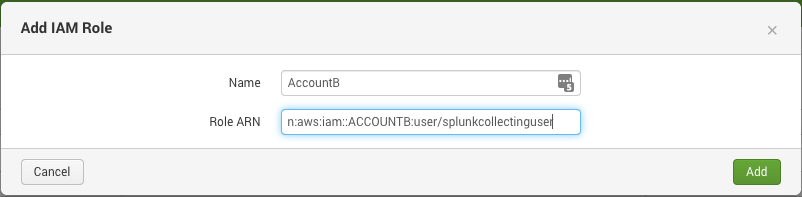
In Splunk, you should add the second account using the arn for Account B "arn:aws:iam::ACCOUNTB:user/splunkcollectinguser" .
Go to your Splunk Add-on for AWS, click on Configuration then click on the IAM Role tab and click the "Add" button. Give the name to this account and paste the ARN. Now, this account will be available for you to AssumeRole and collect data from Account B.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@albertlepinski Are you using the Splunk Addon for AWS on an instance that has the ability to assume the role in account B? If so, you should be able to configure the role to assume here: https://docs.splunk.com/Documentation/AddOns/released/AWS/Setuptheadd-on under Manage IAM Roles. Assuming all of the IAM permissions are setup correctly, what you're looking to do is 100% possible with Splunk and the AWS Addon.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@jokemp I was under the impression that the Splunk Addon does not support external id when assuming a role. Is that not correct?
We did not see anywhere to put the external id.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We do not support external ID with this Add-on. That being said, the way you are supposed to setup the multi-account solution :
1) Create the Splunk IAM Policy in both the master account (Account A) and the sub account (Account B)
2) Create an IAM User from the master account (Account A) and use the access / secret key as the Account under the AWS Add-on Account tab
3) Create an IAM Role in Account B which trusts Account A and has the Splunk Policy attached to it
4) Use the ARN for Account B IAM Role under the IAM Role tab in the Add-on for AWS
5) Setup the inputs with the Master Account A User Account, then select the AssumeRole for the Account B Role.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes yes yes....this is exactly my situation except that step 3 has an external id associated with the IAM Role's trust policy.
This Account B is out of my hands and all our other processes are working just fine assuming the role with the external id so there won't be any changing it to a less secure model.
Thanks for all the help and brain storming but it doesn't look like this Add-on will work for us in this situation. We will have to write a script to pull the logs and then ingest them into Splunk afterwards.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Can Splunk use an External ID if it is required to assume the Role ARN for ACCOUNTB?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
No, we do not support External ID for the AssumeRole function.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Seeing that the post is from 2019, is that still the case that the add-on doesn't support External IDs?
Thanks
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you so much for the fast reply but it is a bit confusing.
You say "No" but then you say "we do". Did you mean "We don't support External ID for the AssumeRole function"?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Fixed my previous response to do not.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thank you for the clarification and speedy response. Have a great day!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
One last question. Can Splunk use a session token?
When I get temporary credentials it has key, access key and session token but I don't see any way to setup a connection/account using these temporary credentials since there is no where to put a session token.
Thank you in advance.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You don’t need the session token. When using the stsAssumeRole you don’t need the access or session token.
I don’t understand what you are trying to do with the session key.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
We use external id's when assuming a role in another account. Unfortunately Splunk does not support the external id so I tried to do the assume that role by hand but it returns key, access key and session token. So I was blocked again because there is no where to put in the session token returned with these temporary credentials when trying to set up a connection.
Here is the back story:
We have an account lets call it A. I have a role I can assume in another account from A, we will call that account B. The only access I have to B is via that role that was setup for us to assume from A. I would like Splunk to be able to pull in logs from B but it seems both approaches, having Splunk assume the role or using the temporary credentials I can obtain by manually assuming the role, are not supported.
Is there another way you can think of?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Is there any update to this ?
I dont think any company allow use of secret/access keys. For the exact scenario mentioned above
We have an account lets call it A. I have a role I can assume in another account from A, we will call that account B. The only access I have to B is via that role that was setup for us to assume from A. I would like Splunk to be able to pull in logs from B.
Does this require me to first add Acct B in splunk by providing secret/access key ? Right now when i try to do assume role it isnt allowing me to do so atleast via console.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@cuyose - Did that help? If so, you can let us know by accepting the answer (you should see a link).