- Apps and Add-ons
- :
- All Apps and Add-ons
- :
- Combine ldapsearch with simple search
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Combine ldapsearch with simple search
Hi!
I'm trying to combine ldapsearch with a simple search
Here is my query:
|ldapsearch domain="domain_name" search="(objectSid=$added_by$)" attrs=cn |table added_by
[|search index=windows_audit EventCode=4732 | eval added_by=mvindex(Security_ID,0) | eval Sid=mvindex(Security_ID,1)]
The idea is to find CN by Sid using ldapsearch function.
But I got an error Error in 'table' command: Invalid argument: 'Account_Domain=domain_name'
Query like:
|ldapsearch domain="domain_name" search="(objectSid="some_sid")" attrs=cn |table cn
Is working perfect on my splunk.
What am I doing wrong?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Please disregard my previous message. I was able to find the information on ldapsearch command at https://docs.splunk.com/Documentation/SA-LdapSearch/3.0.3/User/Theldapsearchcommand
However I am curious if anyone has worked with ADFineGrainedPasswordPolicy and have been able to return users that are in this Policy using ldapsearch. Thanks in advance.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Putting square brackets around part of query is like putting parentheses around part of a math equation - it makes that part go first with the result replacing what was inside. That's why the table command is reporting an invalid argument. You'll have to rearrange the query a little to get the desired result.
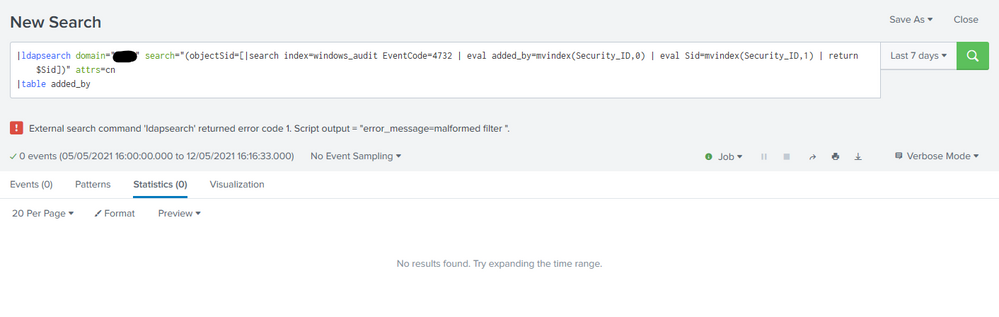
|ldapsearch domain="domain_name" search="(objectSid=[|search index=windows_audit EventCode=4732 | eval added_by=mvindex(Security_ID,0) | eval Sid=mvindex(Security_ID,1) | return $added_by])" attrs=cn
|table added_byIf this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
This returns External search command 'ldapsearch' returned error code 1. Script output = "error_message=malformed filter
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Run the subsearch by itself to see what it returns. Then add eval or other statements as necessary to make the returned value conform to what your LDAP provider expects.
If this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Thanks!
I think soon I get the solution. Now I need to get rid off Sid="...", right?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Yes, and you can do that using return $Sid, as in my original answer.
If this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
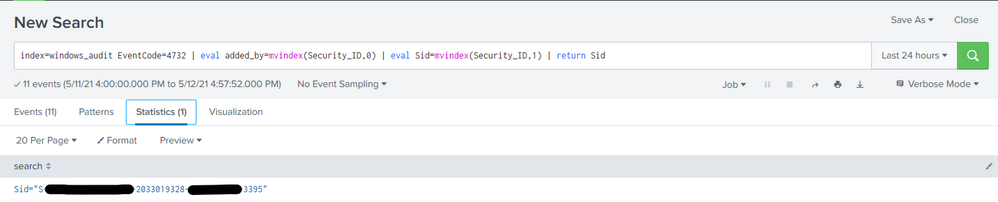
I don't know why but query
index=windows_audit EventCode=4732 | eval added_by=mvindex(Security_ID,0) | eval Sid=mvindex(Security_ID,1) | return $Sid return only 1 result, and then i use your original answer i got
Is there possible to use |ldapsearch domain="my_domain" search="(&(objectSid="[|search index=windows_audit EventCode=4732 | eval added_by=mvindex(Security_ID,0) | eval Sid=mvindex(Security_ID,1) | return Sid]"))" attrs=cn
|table cn, Sid
For several results in sub-search?
Thank you!
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
The return command returns a single result by default. You can add a number to say how many results to return, however, doing so may not give the desired results. For example,
| return 1000 $Sidwill return a string like this
((Sid="\"S-1-5-21-1778430667-2033019328-1848965733-3395\"") OR ( Sid="\"S-1-5-21-1778430667-2033019328-1848965733-3396\"") OR ...)which I believe is not the correct syntax for LDAP.
If this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
I decided to rewrite my query
now i'm doing:
| ldapsearch domain=my_domain search="(&(objectClass=user)(!(objectClass=computer)))" attrs="objectSid,sAMAccountName" | outputlookup Ldap.csv
and then do my main search
Do you now how can I run this by a cron?Shoud i use alert function to schedule this search?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Make it a scheduled report rather than an alert.
If this reply helps you, Karma would be appreciated.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Is there a document or reference of all the available and supported ldapsearch commands?
Thanks in advance.