- Apps and Add-ons
- :
- All Apps and Add-ons
- :
- Boss of SOC V1 dataset: Why am I having a problem ...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Boss of SOC V1 dataset: Why am I having a problem finding an event that I know is there?
Hi Everyone,
I am practicing the event and having problem doing search on the dataset. When I just search the answer, I can see the event, but when I use Splunk search query, the answer is not appearing for some reason.
Question:
What is the name of the file that defaced the imreallynotbatman.com website? Please submit only the name of the file with extension (For example "notepad.exe" or "favicon.ico")
Answer is poisonivy-is-coming-for-you-batman.jpeg
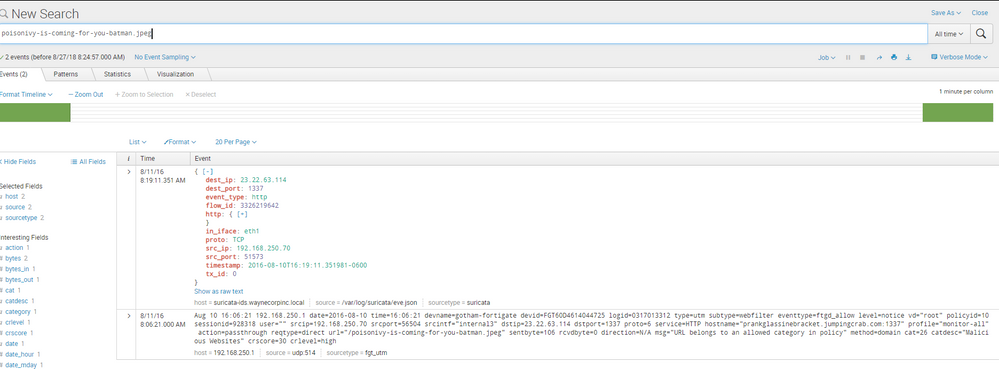
so if I just search poisonivy-is-coming-for-you-batman.jpeg it gives me two events
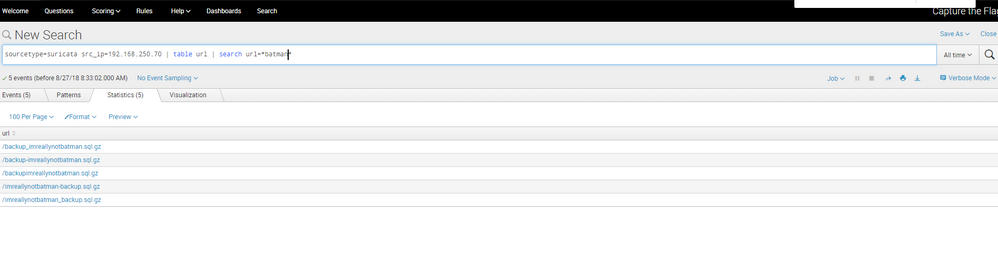
However when I do search sourcetype=suricata src_ip=192.168.250.70 | table url | search url=*batman* it does not give me that event and this happens to a lot of questions. Any suggestions of what is happening?
updated to mark code for you - dmj
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @samlinsongguo. Did either of the answers below solve your question? If yes, please click “Accept” directly below the answer to resolve the post. If not, please comment with more information if you are still having issues.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
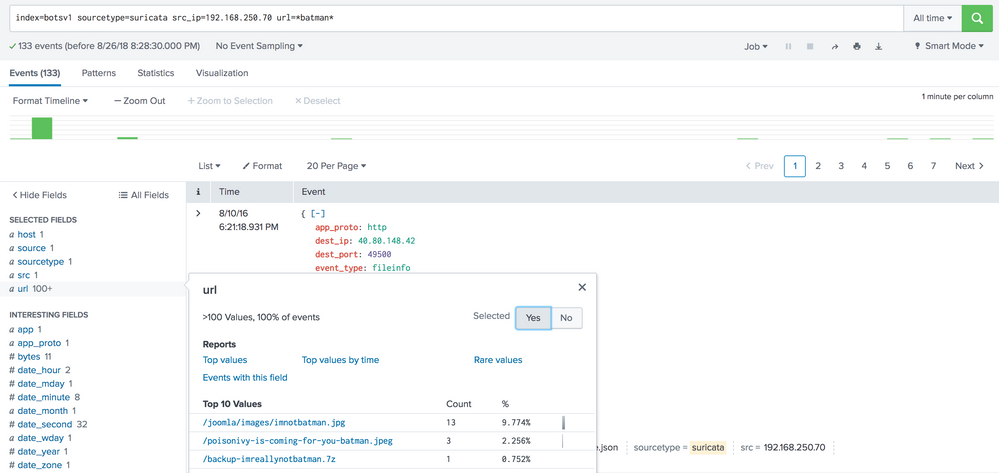
I don't have a great answer for you at the moment... I have attached my searches of sourcetype suricata in two different ways and both ways return 133 events.
It is worth mentioning that when I run a search for poisonivy-is-coming-for-you-batman.jpeg, i get 10 events returned, but you are only getting two. I wonder if your dataset is not complete for some reason. The other thing that is odd is you are showing me the first and last event in your first search.
I wish I had a better answer for you but hopefully these couple of nuggets help steer you toward the expected output.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Take a careful look at exactly what you are specifying in your search, especially the exact spelling of each field.
Review each of the results from your first search, look in those results for the fields that are spelled exactly like you spelled them, and see whether they exist and what values they contain.
If you do this carefully, you will see what mistake you made.
(We could tell you, but you will learn more by finding them yourself.)
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi DalJeanis
I am not quick get it it I triple checked the first search is "poisonivy-is-coming-for-you-batman.jpeg" and the second query is search sourcetype=suricata src_ip=192.168.250.70 | table url | search url=*batman* if you refer to the actual field is http.url I did the same search as well search sourcetype=suricata src_ip=192.168.250.70 | table http.url | search http.url=*batman* it have the same problem. plus I can see both field have the value.