- Splunk Answers
- :
- Using Splunk
- :
- Alerting
- :
- Can I write a single search for populating summary...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi,
Wanted to know if we can have a single search to populate the summary index and also to create an alert based on the search results.
We have a search for windows event logs for servers to see if some event has occurred.
index=main | stats count by host| eval health=if(count > 1," RED", "GREEN")
We want to write both GREEN and RED events to the summary table but want to alert only for RED ones, is it possible to do this with just one search or shall we create two different searches?
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
hello there,
the answer is yes, however, before you proceed, consider the following search as it will be super fast and can be ran on very long periods of time without need to summarize:
| tstats count where index=main by host
| eval health=if(count > 1," RED", "GREEN")
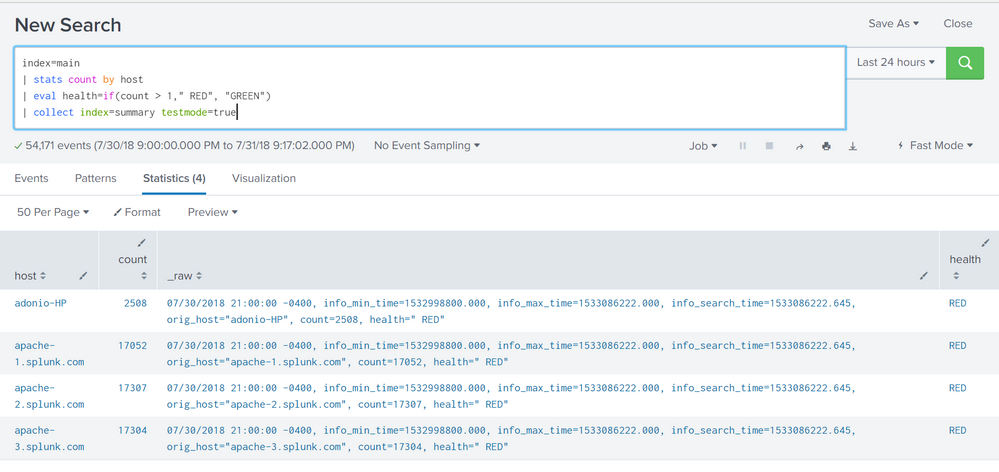
run a search with the collect command to collect data to summary index, see example below with testmode=true
index=main
| stats count by host
| eval health=if(count > 1," RED", "GREEN")
| collect index=summary testmode=true
screenshot:
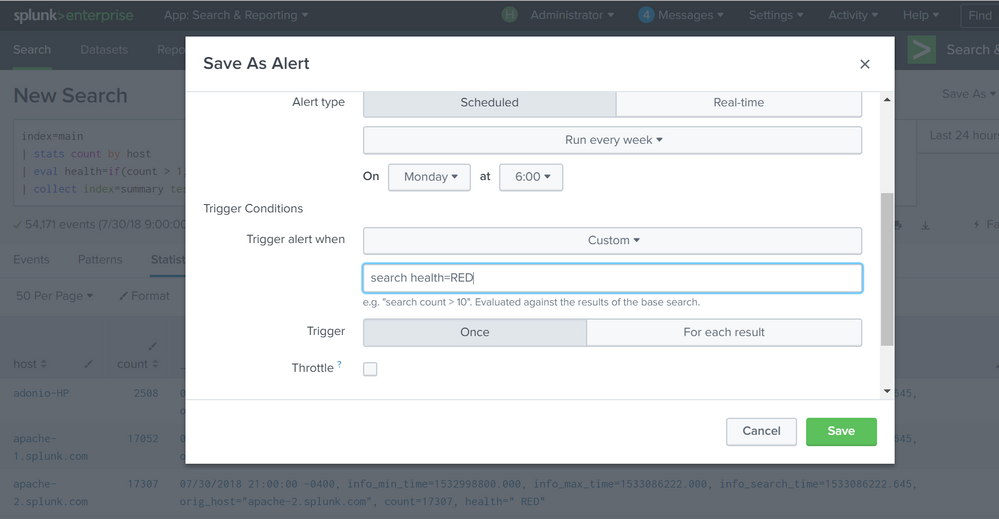
save as alert and add condition, screenshot:
configure to run every X interval and it will populate your summary index and alert if condition met
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
hello there,
the answer is yes, however, before you proceed, consider the following search as it will be super fast and can be ran on very long periods of time without need to summarize:
| tstats count where index=main by host
| eval health=if(count > 1," RED", "GREEN")
run a search with the collect command to collect data to summary index, see example below with testmode=true
index=main
| stats count by host
| eval health=if(count > 1," RED", "GREEN")
| collect index=summary testmode=true
screenshot:
save as alert and add condition, screenshot:
configure to run every X interval and it will populate your summary index and alert if condition met