- Splunk Answers
- :
- Using Splunk
- :
- Alerting
- :
- Re: Can I set an alert in splunk where the event i...
- Subscribe to RSS Feed
- Mark Topic as New
- Mark Topic as Read
- Float this Topic for Current User
- Bookmark Topic
- Subscribe to Topic
- Mute Topic
- Printer Friendly Page
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Object:
Object Server: Security
Object Type: File
Object Name: \Device\HarddiskVolume54\Tax\Confidential
Handle ID: 0x1110
Resource Attributes: S:AI
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @akim08,
could you share an example of your logs?
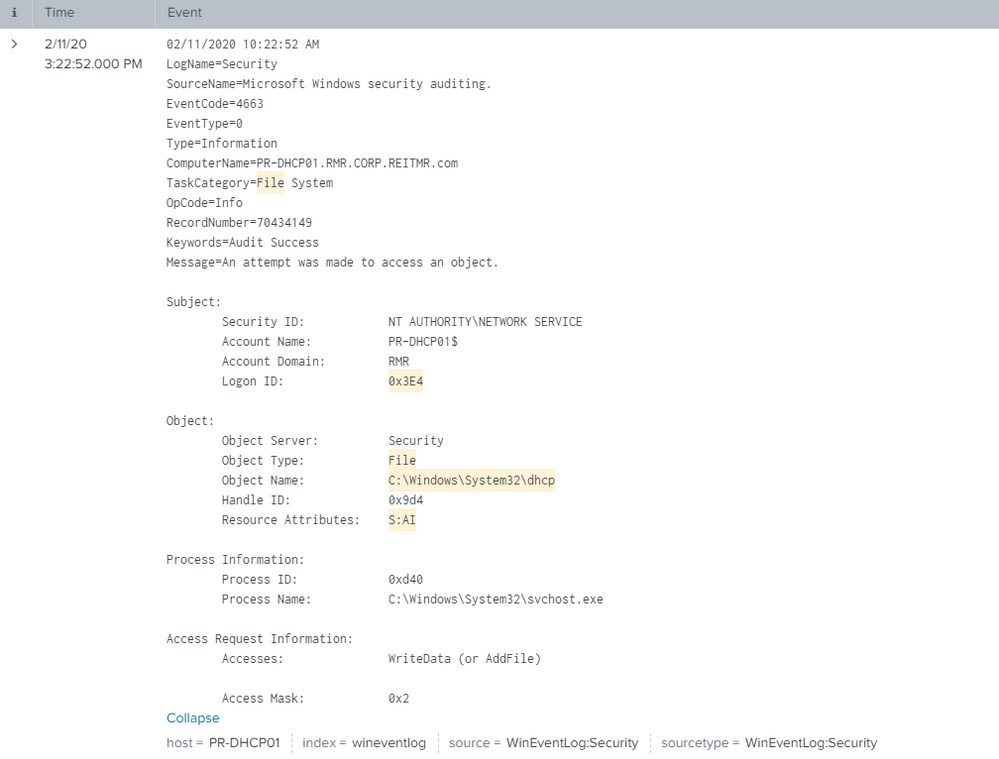
you have to extract the fields in a multiline log (Windows eventlogs), I use anothen eventcode and my windows is in italian, but the approach is the correct one:
e.g. if you have something like this
02/11/2020 04:23:45 PM
LogName=Security
SourceName=Microsoft Windows security auditing.
EventCode=4624
EventType=0
Type=Informazioni
ComputerName=DESKTOP-KBVMP9Q
TaskCategory=Logon
OpCode=Informazioni
RecordNumber=206682
Keywords=Controllo riuscito
Message=Accesso di un account riuscito.
Soggetto:
ID sicurezza: S-1-5-18
Nome account: DESKTOP-KBVMP9Q$
Dominio account: WORKGROUP
ID accesso: 0x3E7
and you want to extract ID_sicurezza, Nome_account and ID_accesso, you shuld use a multiline regex like this:
(?ms)ID sicurezza:\s+(?<ID_sicurezza>[^ ]*)\s*Nome account:\s+(?<Nome_account>[^ ]*)Dominio.*\s+ID accesso:\s+(?<ID_accesso>[^ ]*)
that you can test at https://regex101.com/r/KCuFj4/1
Ciao.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @akim08,
could you share an example of your logs?
you have to extract the fields in a multiline log (Windows eventlogs), I use anothen eventcode and my windows is in italian, but the approach is the correct one:
e.g. if you have something like this
02/11/2020 04:23:45 PM
LogName=Security
SourceName=Microsoft Windows security auditing.
EventCode=4624
EventType=0
Type=Informazioni
ComputerName=DESKTOP-KBVMP9Q
TaskCategory=Logon
OpCode=Informazioni
RecordNumber=206682
Keywords=Controllo riuscito
Message=Accesso di un account riuscito.
Soggetto:
ID sicurezza: S-1-5-18
Nome account: DESKTOP-KBVMP9Q$
Dominio account: WORKGROUP
ID accesso: 0x3E7
and you want to extract ID_sicurezza, Nome_account and ID_accesso, you shuld use a multiline regex like this:
(?ms)ID sicurezza:\s+(?<ID_sicurezza>[^ ]*)\s*Nome account:\s+(?<Nome_account>[^ ]*)Dominio.*\s+ID accesso:\s+(?<ID_accesso>[^ ]*)
that you can test at https://regex101.com/r/KCuFj4/1
Ciao.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@gcusello can you take a look?
Thanks
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @akim08,
try this:
(?ms)Subject:.*Logon ID:\s+(?<Logon_ID>[^ ]*)\s+Object.*Object Type:\s+(?<Object_Type>\w+)\s+Object Name:\s+(?<Object_Name>[^ ]*).*Resource Attributes:\s+(?<Resource_Attributes>[^ ]*)\s+ Process Information:
(if you can share the example in text I can use regex101 to show you the regex).
When you have the fields you can create your filters.
Ciao.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hey @gcusello, Do i have to do it this way? I just extracted the fields and they are already there, i.e. Object_Name, Object_Type. But when I try Object_Name = C:\Windows\System32\dhcp\j50tmp.log .....it will not search for that item.
I can search other items such as:
Object_Type = File
Object_Server = Security
But not the Object_Name.
I am trying to create an alert where It will alert me with those categories in mind.
Thanks.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @akim08,
did you tried to use quotes?
Object_Name = "C:\Windows\System32\dhcp\j50tmp.log"
otherwise try
Object_Name = "C:\\Windows\\System32\\dhcp\\j50tmp.log"
Ciao.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@gcusello i now used quotes, and it seems to work.
I am wondering if this will work here as my search request and save as an alert:
sourcetype=WinEventLog:Security EventCode=4663 Object_Type=File Object_Server=Security Object_Name="\Device\HarddiskVolume54\Tax\Confidential" Handle_ID=0x1110 Resource_Attributes="S:AI"
This is my final answer...haha
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Hi @akim08,
I'm happy for you!
if you're satisfied, please, acceèt and/or upvote it for the other people of Community.
Ciao and Next Time.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@gcusello i believe the double \ worked!
Now I am hoping that this is the correct syntax to search an alert such as this one.
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
i did this:
sourcetype=WinEventLog:Security EventCode=4663 Handle_ID=0x8dc host=PR-MA49DHCP01 Object_Type=File Object_Server=Security
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
You can use your idea using the Splunk full text search features but it's very slow, so you should see how many events you have.
Ciao.
Giuseppe
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
@gcusello i see, so doing it that way will slow things down
- Mark as New
- Bookmark Message
- Subscribe to Message
- Mute Message
- Subscribe to RSS Feed
- Permalink
- Report Inappropriate Content
Please see below gcusello